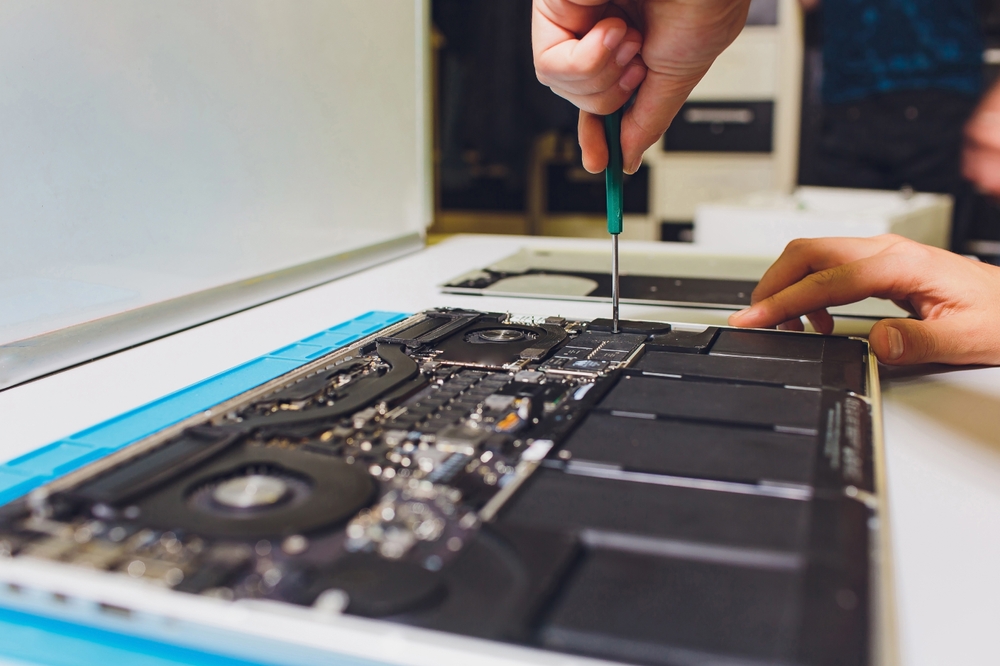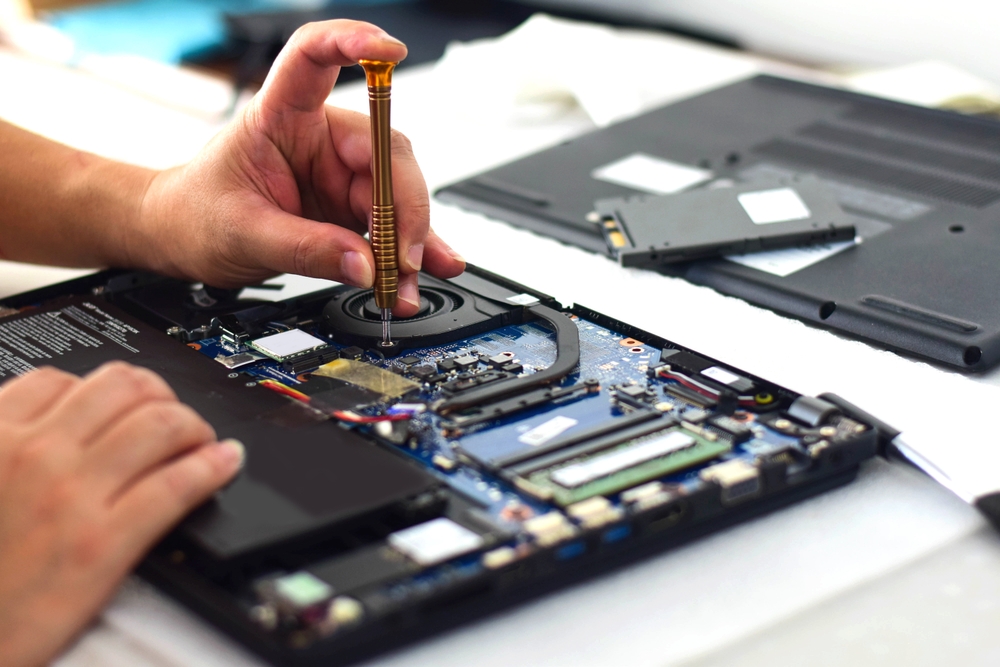
Computers are the backbone of small businesses. Whether you run a real estate office in Scottsdale or a boutique marketing agency in downtown Phoenix, your daily operations likely depend on a network of devices, software, and cloud tools. But while many small business owners prioritize customer service, sales, and product development, they often overlook a […]